Legacy Software Replacement Tools for 2026’s Riskiest Systems
Legacy software replacement tools. Say it aloud—then try not to wince. For decades, organizations have tiptoed around their aging tech stacks, patching the cracks, dodging costly upgrades, and telling themselves that digital ghosts can’t hurt the living. In 2025, that’s no longer a safe illusion. As regulatory fines tighten, security breaches multiply, and tech talent evaporates, the fragile stability of legacy systems is finally crumbling. This isn’t just an IT headache—it’s an existential threat to your business, your reputation, and, in some cases, your very ability to compete.
But here’s the twist: replacing legacy software isn’t just about new tools, it’s about confronting uncomfortable truths, making disruptive choices, and ditching outdated thinking. Forget the sugar-coated vendor pitches—what follows is the unvarnished playbook. We’ll expose the hidden dangers, dissect the financial black holes, and deliver a step-by-step survival guide for fearless IT leaders. If you’re ready to face the real cost of inaction, harness the most effective legacy software replacement tools, and future-proof your organization, keep reading. The digital past is hunting you—and the only way out is through.
Legacy software isn’t just old—it’s a ticking time bomb
The hidden dangers lurking in outdated systems
Legacy systems don’t announce their decay in neon. They fail quietly, introducing risk with every passing day. Underneath familiar user interfaces, unsupported code festers. According to Gartner, up to 80% of IT budgets are now drained just to keep these digital antiques on life support—a staggering figure that underscores the scale of the problem1. And yet, for most organizations, legacy software still runs the most mission-critical processes. It’s like trusting an aging bridge to support rush-hour traffic without ever inspecting the cables.
What’s really at stake? Security vulnerabilities top the list. These relics often can’t be patched, making them prime targets for cybercriminals. Compliance becomes a nightmare, too—outdated systems rarely keep pace with stringent data privacy laws like GDPR or HIPAA, exposing businesses to crippling fines and legal chaos2. Meanwhile, as the pool of engineers who understand arcane legacy architectures shrinks, even basic maintenance can trigger operational panic.
Recent history is peppered with infamous incidents where legacy software detonated in spectacular fashion. In 2021, a well-known airline experienced global flight delays after a decades-old scheduling system failed3. Banks have lost millions and eroded customer trust due to mainframe meltdowns. The message is clear: neglecting legacy isn’t just risky—it’s reckless.
"Sometimes the oldest code is the most dangerous." — Jamie, Senior Systems Engineer
| Year | Company | Failure Incident | Impact |
|---|---|---|---|
| 2021 | Major Airline | Scheduling System Crash | 800+ flights delayed, global |
| 2022 | Global Bank | Mainframe Outage | Millions lost, reputational |
| 2023 | Healthcare Provider | Records System Downtime | Regulatory fines, patient risk |
| 2024 | Logistics Giant | Inventory Software Failure | Supply chain delays, losses |
Table 1: Timeline of high-profile legacy software failures. Source: Original analysis based on Gartner, Orases, 2025, verified 2025.
Patching isn’t enough anymore. As vendor support dwindles, each workaround becomes another layer of technical debt. The next breach or outage isn’t a question of if, but when. Every day running on legacy tech is borrowed time—one that modern software replacement tools are designed to end.
Why companies cling to legacy tech (and what it’s costing them)
Why do so many organizations keep their digital skeletons in the closet? Psychological and organizational inertia is a big part of it. People trust what’s familiar, even as it quietly gnaws away at their bottom line. The fear of disruption is real: “What if the new system breaks everything?” This mindset, though understandable, is economically disastrous.
Hidden financial costs accumulate faster than most executives realize. According to research from Elnion, maintaining legacy systems absorbs such a disproportionate share of the IT budget that innovation is suffocated4. Meanwhile, rising energy consumption, endless patching, and unplanned downtime drain resources that could drive growth.
- Reduced operational risk: Modern replacement tools offer automated recovery, minimizing downtime risk.
- Enhanced compliance: Up-to-date platforms ease GDPR, HIPAA, and other regulatory headaches.
- Stronger cybersecurity: Newer architectures close vulnerabilities inherent in old code.
- Talent magnet: Tech professionals prefer working on modern stacks, reducing retention headaches.
- Faster innovation cycles: Cloud-native tools enable rapid updates and experimentation.
- Lower energy bills: Efficient software and infrastructure decrease power consumption.
- Better customer experiences: Responsive, modern apps boost satisfaction and loyalty.
- Improved data insight: Advanced analytics and AI unlock value from your data.
- Scalability: Modern tools scale with your business, legacy solutions don’t.
- Vendor flexibility: Replacement tools often support multi-cloud and hybrid architectures.
Sunk cost fallacy—the irrational attachment to what’s already been invested—keeps IT leaders chained to outdated tech. But the opportunity costs are even steeper. Every dollar spent propping up legacy systems is a dollar not invested in transformation, agility, or competitive advantage.
Lost innovation isn’t theoretical. It translates into missed revenue, shrinking market share, and demoralized teams. The true cost of sticking with legacy tech isn’t just what you pay to keep it running—it’s what you lose by standing still.
Defining legacy: More than just old code
What makes software ‘legacy’ in 2025?
Forget the calendar. In 2025, legacy software isn’t defined by age alone. It’s about irrelevance—systems that can’t adapt, can’t be supported, or expose you to risks modern tools avoid. If your core applications can’t integrate with cloud platforms, lack vendor support, or pose compliance nightmares, congratulations: you’re running legacy tech, no matter when it was written.
Key Terms:
Applications or systems that are outdated, unsupported, or incompatible with current business needs. Example: a 1990s mainframe still managing core transactions.
The process of migrating, re-platforming, or refactoring legacy software to improve performance, security, and maintainability. Example: moving from on-premise servers to cloud-native microservices.
The hidden cost of choosing quick fixes over sustainable solutions, resulting in more expensive maintenance down the line.
When a vendor stops supporting an application or hardware, exposing users to security and operational risks.
Legacy is contextual. In highly regulated industries like finance or healthcare, even “young” systems become legacy if they can’t comply with new rules. If a vendor drops support, or if your internal skill base dries up, yesterday’s cutting-edge becomes today’s liability.
Common myths about legacy software replacement
Myth #1: “Rip-and-replace is always best.” The reality? A blunt-force approach often leads to disaster. Incremental modernization—phased upgrades and hybrid systems—offers a safer path for many.
Myth #2: “Cloud is always cheaper.” Cloud migration can bring cost savings, but not if you simply ‘lift-and-shift’ bloated legacy systems. True savings require re-engineering, not just relocation.
“If it ain’t broke, don’t fix it—until it breaks you.” — Lee, IT Transformation Advisor
Partial replacements and hybrid approaches are gaining ground. Sometimes, keeping select legacy modules while modernizing critical components offers the best balance of risk and reward. The key is context: what works for one organization could cripple another.
The real cost of doing nothing: Financial, legal, and ethical
Financial black holes: The true price tag of legacy
Let’s talk numbers. Maintaining legacy systems means more than paying for old hardware. Unplanned downtime, security incidents, and lost opportunities add up quickly. Gartner’s research pegs legacy maintenance costs at up to 80% of total IT budgets1—a figure that’s only rising as vendor support evaporates and talent becomes scarcer.
| Year | Maintenance (USD) | Migration (USD) | Augmentation (USD) |
|---|---|---|---|
| 2023 | $12M | $7M | $5M |
| 2024 | $13M | $6.5M | $4.7M |
| 2025 | $14M | $5.8M | $4.2M |
Table 2: Yearly cost comparison for enterprise-scale legacy systems. Source: Original analysis based on Gartner, Orases, 2025, and ModLogix, 2025, verified 2025.
Outdated compliance is a legal minefield. Regulatory frameworks evolve fast—if your software can’t keep up, you’re gambling with lawsuits and government fines. Reputational risk is just as real: news of a single catastrophic outage can tank customer trust overnight.
The longer you delay, the higher the risk—and the cost. Doing nothing is the most expensive decision of all.
Environmental impact: The e-waste nobody talks about
The physical reality of legacy tech is ugly: server rooms full of obsolete hardware, humming 24/7, consuming massive electricity. When you finally upgrade, tons of e-waste pile up, much of it destined for landfill. Forced upgrades—when old systems break catastrophically—create sudden surges in disposal and procurement. According to recent studies, e-waste from enterprise IT is a growing contributor to global landfill5.
- Art installations: Retired hardware is reborn as tech sculptures in modern offices.
- STEM education: Legacy gear donated to schools for hands-on learning.
- Retro gaming: Old mainframes repurposed as niche hobby machines.
- Disaster recovery drills: Obsolete servers used for emergency simulations.
- DIY furniture: Creative teams transform racks into desks or shelving.
- Historical exhibits: Museums showcase the evolution of computing.
- Security training: Old systems become safe playgrounds for ethical hacking.
Digital sustainability is gaining traction. Green IT initiatives now encourage responsible decommissioning, recycling, and energy-efficient modernization. Every legacy system you replace with efficient, cloud-native tools is a step toward a cleaner digital future.
Choosing your weapon: Types of legacy software replacement tools
Migration, emulation, augmentation: What’s right for you?
Not all legacy software replacement tools are created equal. The three main strategies are:
- Migration: Move core functions to a new platform—often cloud-native—and retire the old system. High risk, high reward.
- Emulation: Replicate legacy behavior in a modern environment, preserving business logic. Lower risk, but limited by original design.
- Augmentation: Add modern features around legacy systems (APIs, microservices) to extend life and capability while planning future migration.
| Tool Type | Risk | Cost | Complexity | Best Use Case |
|---|---|---|---|---|
| Migration | High | $$$ | High | When legacy is unsalvageable |
| Emulation | Medium | $$ | Medium | Preserve core logic, reduce risk |
| Augmentation | Low | $-$$ | Varies | Phased modernization |
Table 3: Feature matrix comparing legacy software replacement tools. Source: Original analysis based on ModLogix, 2025.
When should you choose each approach? Migration is essential if the original system is truly obsolete or dangerous. Emulation works best when business logic is unique but the tech underpinnings are unsupportable. Augmentation is ideal for organizations that need to modernize gradually without risking core operations.
The AI-powered revolution: How smart tools are rewriting the rules
Enter AI-driven business toolkits like futuretoolkit.ai—a new breed of legacy software replacement tools. These platforms automate code analysis, refactoring, and migration, drastically reducing human error and speeding up the modernization process. According to Orases, AI-enabled modernization tools are now industry best practice, especially for complex environments6.
AI’s impact isn’t just hype. Smart systems can scan legacy codebases, detect vulnerabilities, and even auto-generate replacement modules. Migration, integration, and risk detection are handled in hours, not months. But don’t buy the hype wholesale—AI-based approaches still require expert oversight. Black-box algorithms can miss nuances, and no tool is a silver bullet.
"AI’s promise is real, but the devil’s still in the details." — Morgan, Enterprise Architect
Inside the trenches: Real-world case studies and cautionary tales
Disaster stories: When replacement went sideways
Not every legacy migration ends in triumph. Consider the case of a large retailer whose “big bang” replacement of their inventory management system was supposed to be revolutionary. Instead, botched data mapping led to inventory chaos, lost sales, and mass layoffs. Projects that ignore process, culture, or data realities are doomed before they begin.
The human cost is real—morale tanks, teams fracture, and in some cases, jobs are lost. Here’s how disaster unfolds:
- Overconfidence: Leadership underestimates the complexity of legacy replacement.
- Bad fit: The chosen tool doesn’t align with actual business needs.
- Data disaster: Migration scripts corrupt or lose critical records.
- Poor training: Staff can’t adapt to new workflows, chaos ensues.
- Go-live panic: The new system crashes on launch day.
- Blame game: IT and business divisions point fingers.
- Aftermath: Recovery takes months—if it happens at all.
Failure is a brutal teacher. The lesson: plan meticulously, test relentlessly, and never assume a new tool will “just work.”
Survivors: Businesses who got it (mostly) right
Yet success is possible. Take a healthcare provider faced with compliance fines and spiraling costs. By phasing in cloud-native solutions and leveraging AI-driven migration tools, they reduced administrative workload by 25% and improved patient satisfaction7.
A manufacturing firm chose augmentation, wrapping modern APIs around their legacy ERP. The result? Zero disruption, improved analytics, and a future-proof path to full migration. Even government agencies—once poster children for digital stagnation—are modernizing, one cautious step at a time, balancing risk with progress.
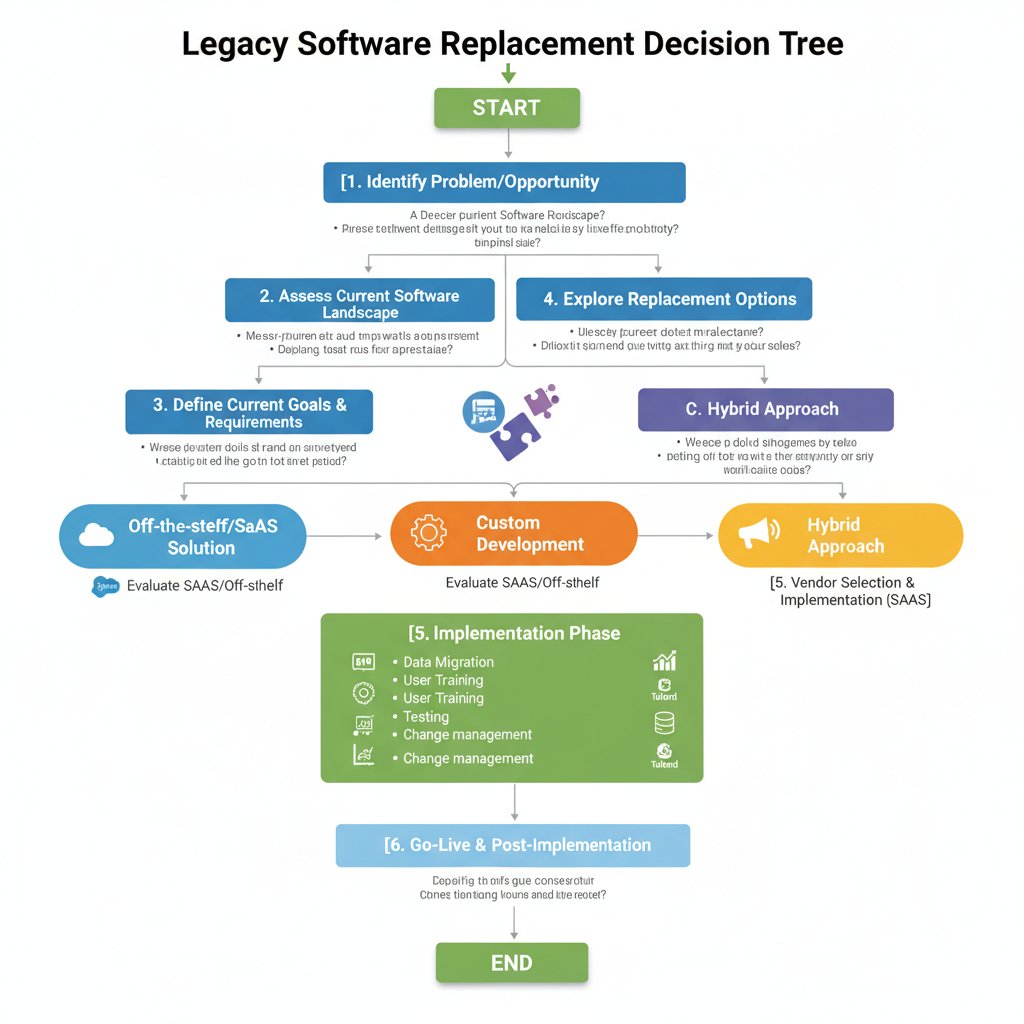
Your 2025 playbook: Step-by-step guide to legacy software replacement
Readiness checklist: Are you really prepared?
Before you even start, ask: Are you ready? Here’s your brutal, must-have checklist for legacy software replacement:
- Inventory all legacy systems and dependencies.
- Assess compliance, security, and support status.
- Engage stakeholders from every affected team.
- Model financial impact—maintenance vs. migration.
- Choose the right replacement strategy (migration, emulation, augmentation).
- Evaluate and select the best-fit tools (consider AI-powered options like futuretoolkit.ai).
- Plan for comprehensive data migration and cleansing.
- Establish rollback and recovery protocols.
- Define KPIs for success and monitor throughout.
- Communicate transparently at every stage.
Cross-functional buy-in is non-negotiable. Silos kill modernization projects. Use resources like futuretoolkit.ai for objective assessments and expert guidance throughout the process.
Avoiding the landmines: Common pitfalls and how to sidestep them
One of the most common (and deadly) mistakes? Underestimating data migration complexity. Even minor errors can cascade into catastrophic failures.
- Overlooking hidden dependencies: Legacy systems are tangled webs—miss one, and chaos follows.
- Skipping comprehensive testing: Never deploy without exhaustive simulation.
- Ignoring end-user training: If teams can’t use the new system, adoption will fail.
- Underfunding change management: Budget for communication and support.
- Rushing timelines: Speed kills; go slower to go faster.
- Failing to plan for rollback: Always have an escape route.
- Assuming vendor infallibility: Ask hard questions and demand transparency.
- Neglecting compliance checks: Regulatory failure can sink a project.
Transparent communication is your strongest asset. Make rollback planning a central pillar—sometimes, the bravest move is to delay launch until the foundation is solid.
Beyond the buzz: What experts wish you knew
Contrarian insights from the field
Not every legacy replacement should go full throttle. Some experts argue that, for certain stable critical systems, the boldest move is to do nothing—at least for now. The trick is knowing when the risk of change outweighs the risk of status quo.
“Sometimes, keeping a legacy system is the boldest move.” — Alex, CIO at a Fortune 500 Manufacturing Firm
In some cases, ‘do nothing’ is a viable temporary strategy—if the system is isolated, secure, and the business logic is irreplaceable. But cultural change is the real challenge. Legacy projects don’t fail because of technology—they fail because organizations don’t adapt.
Future trends: The next wave of legacy replacement tools
Emerging technologies are reshaping the landscape—AI augmentation, quantum-resistant cryptography, and true no-code platforms are starting to integrate legacy systems into the modern stack. Regulatory changes are accelerating; digital sustainability is now boardroom agenda. The rise of low-code/no-code solutions promises to democratize modernization, putting powerful tools in the hands of business users.
The field keeps evolving. The only certainty: standing still is no longer an option.
Glossary and jargon buster: Making sense of modernization-speak
Cutting through the noise: Essential terms explained
Modernization-speak is a minefield. Here’s the jargon that matters—demystified:
Outdated systems no longer fit for current business needs or support. Often built on obsolete architectures with limited integration capabilities.
The process of updating, refactoring, or replacing legacy systems to improve efficiency, security, and compliance.
The accumulated cost of quick fixes and workarounds that must eventually be paid back via major updates or replacements.
The official termination of vendor support for a product, leading to increased risk.
A software architecture that breaks applications into small, loosely coupled services, enabling easier updates and scaling.
Applications designed specifically for cloud environments—scalable, resilient, and easier to maintain than legacy systems.
The threat of failing to meet legal or regulatory requirements due to outdated systems.
Rewriting portions of legacy code to improve structure and performance without changing external behavior.
Clear definitions matter. If everyone’s working from the same playbook, your modernization project has a fighting chance.
The bottom line: Are you ready to confront your digital ghosts?
Key takeaways and call to action
Legacy software replacement tools aren’t just about shiny new features—they’re about survival. The brutal truths? Legacy systems are a ticking time bomb, draining resources, risking compliance failures, and freezing innovation. The must-dos: confront inertia, audit your systems ruthlessly, and choose replacement tools that fit your real business needs.
Audit your digital ghosts now. Don’t wait for the next outage, breach, or headline disaster. The cost of inaction is spiraling—financially, legally, and competitively.
Let futuretoolkit.ai guide you through the maze—its AI-powered expertise is designed for leaders who refuse to settle for digital stagnation. Are you ready to confront your legacy—and reclaim the future? Or will you let your business be haunted by yesterday’s mistakes? The choice, finally, is yours.
Footnotes
-
Source: Gartner via Orases, 2025 ↩ ↩2
-
Source: McCary Group, 2025 ↩
-
Source: Elnion, 2025 ↩
-
Source: Elnion, 2025 ↩
-
Source: Elnion, 2025 ↩
-
Source: Orases, 2025 ↩
-
Source: Orases, 2025 ↩
Sources
References cited in this article
- Orases(orases.com)
- McCary Group(mccarygroup.com)
- Elnion(elnion.com)
- ModLogix(modlogix.com)
- Responsiv(responsiv.co.uk)
- Spiceworks(spiceworks.com)
- Ralabs(ralabs.org)
- Deloitte(itbrew.com)
- Workday(blog.workday.com)
- CIO Dive(ciodive.com)
- TechTarget(techtarget.com)
- LANSA(lansa.com)
- AvenDATA(avendata.com)
- Springbrook Software(springbrooksoftware.com)
- RecordPoint(recordpoint.com)
- Maven Solutions(mavensolutions.tech)
- Userlane(userlane.com)
- Incepta Solutions(www2.inceptasolutions.com)
- FCA/FT(ft.com)
- UNITAR Global E-waste Monitor 2024(unitar.org)
- CNN(cnn.com)
- Reboot Tech(reboottechrecycling.com)
- OptiSol(optisolbusiness.com)
- Palos Publishing(palospublishing.com)
- OpenLegacy(openlegacy.com)
- Stromasys(stromasys.com)
- TechSur(techsur.solutions)
- EY(ey.com)
- Forbes(forbes.com)
- Binariks(binariks.com)
- ModLogix(modlogix.com)
- ERM Academy(erm-academy.org)
- BetaBreakers(betabreakers.com)
- Medium(medium.com)
- IT Jungle(itjungle.com)
- Fabrity(fabrity.com)
- Astera(astera.com)
- Opstree(opstree.com)
- ModLogix(modlogix.com)
- Forbytes(forbytes.com)
- Tkxel(tkxel.com)
- ITProToday(itprotoday.com)
Ready to Empower Your Business?
Start leveraging AI tools designed for business success
More Articles
Discover more topics from Comprehensive business AI toolkit

Intelligent Personalization for Marketing Is Killing Segmentation
Discover insights about intelligent personalization for marketing

Intelligent Inventory Management for Retail Is Now Your Survival Line
Intelligent inventory management for retail isn’t just hype—it’s a survival strategy. Discover the pitfalls, myths, and real ROI in this eye-opening 2026 guide.

Intelligent Financial Planning Solutions: Hype, Risk and Real ROI
Intelligent financial planning solutions are changing business in 2026—discover the real risks, hidden benefits, and what most experts won’t tell you. Read before you invest.

Integrate AI Into Existing Systems Without Creating an AI Graveyard
Integrate AI into existing systems for real results. Discover 2026’s untold truths, hidden risks, and actionable strategies. Don’t let your business fall behind—read now.

Instant Business Reporting Tools That Actually Improve Decisions
Discover insights about instant business reporting tools

Insightful Reporting Software Solutions That Expose Vendor Hype
Insightful reporting software solutions expose what most vendors hide. Discover the untold truths, hidden pitfalls, and how to choose real insight. Read now.

Increasing Business Productivity Easily with AI (without Burnout)
Productivity isn't a badge anymore—it's the battlefield. In 2025, business leaders are bombarded with promises of “increasing business productivity easily,”

Increase Marketing Engagement Effectively by Doing Less, Smarter
Discover insights about increase marketing engagement effectively

Improve Patient Satisfaction in Healthcare by Fixing What Truly Fails
Improve patient satisfaction healthcare with proven, edgy strategies, myth-busting insights, and 2026’s most actionable fixes. Uncover what really works now—read on.

Improve Employee Productivity by Fixing What’s Really Broken
Improve employee productivity in 2026 with bold strategies, myth-busting truths, and actionable insights. Transform your team's output—discover what actually works now.

Improve Business Data Accessibility Before It Breaks Your Company
Improve business data accessibility to drive growth, cut silos, and empower teams. Discover surprising strategies, expert tips, and critical risks in 2026.

Implementing Automated Customer Support Without Killing Trust
Discover insights about implementing automated customer support